Certificates are used as part of the Transport Level Security (TLS) protocol. They enable using Web browsers, CTERA Edge Filers, and CTERA Agents to verify that the CTERA Portal server with which they are communicating is authentic and not spoofed.
If the CTERA Portal does not have a valid certificate installed, a warning is displayed to the end user when logging a device into the portal, offering the option to proceed anyway.
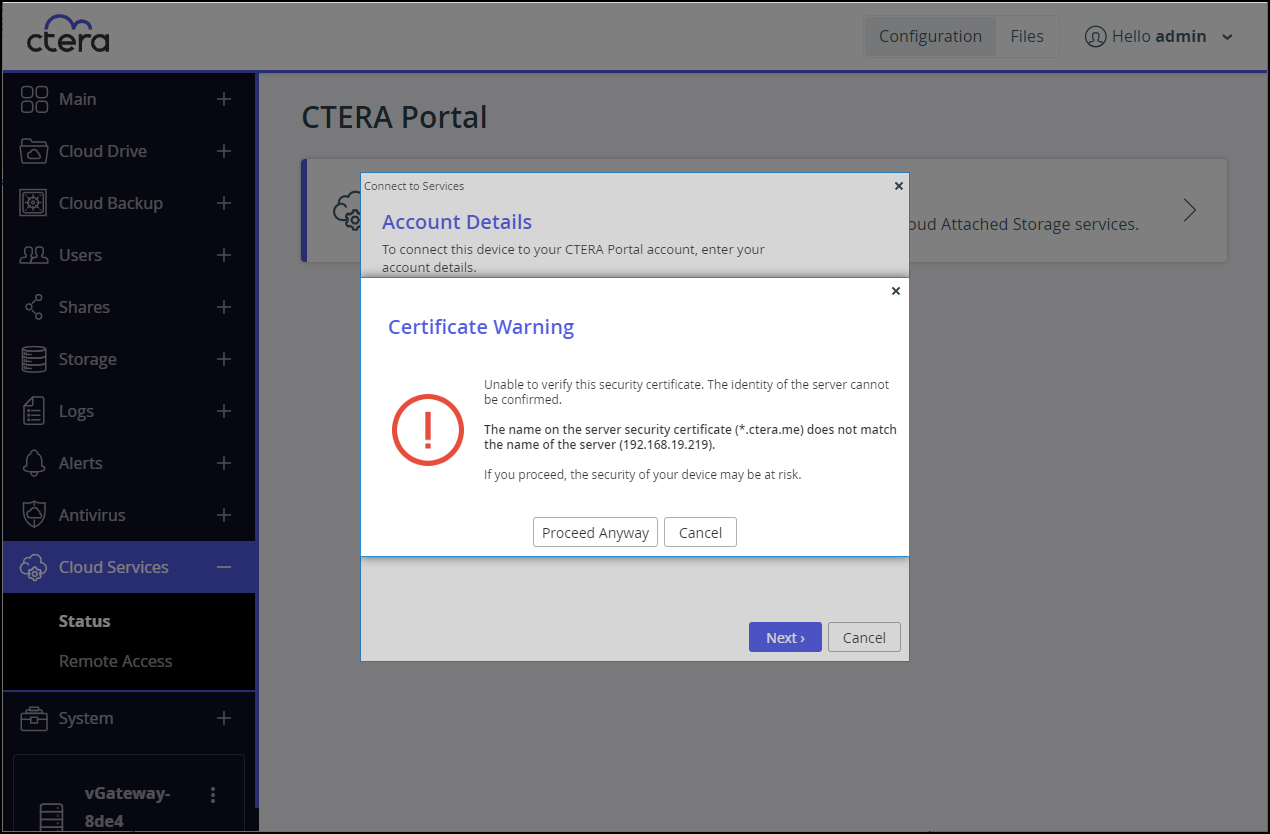
This warning is presented every time a user connects a device to the portal, until a valid certificate is installed.
During the configuration of the primary server, for a production environment, you should have installed a valid certificate, as described in Installing a TLS Certificate.
A valid TLS certificate must meet the following requirements:
- If multiple virtual portals are configured, then each virtual portal has its own DNS name. In this case, the TLS certificate should be a wildcard certificate, that is, the DNS name embedded in the certificate should start with "*". For example, if the CTERA Portal's DNS suffix is myportal.com, and there are two virtual portals, portal1.myportal.com and portal2.myportal.com, you need a wildcard certificate for *.myportal.com.
- If you have only one portal, and do not intend to configure multiple virtual portals, then a regular TLS certificate is preferable and not a wildcard certificate. For example, if your portal's DNS name is portal1.myportal.com, then you need a certificate for portal1.myportal.com.
- It is possible to specify multiple alternative names, using the
subjectAltNamecertificate extension. - The certificate must be in *.zip format and contain certificate files in *.pem format.
You can automatically generate a certificate request to send to any public TLS certificate authority, such as GoDaddy, which CTERA recommends, Verisign, or Thawte, as described in Generate a Certificate Signing Request. Once you have received a certificate from the certificate authority, you can install it, as described in Install the Signed Certificate on CTERA Portal.
Alternatively, you can export a certificate from another portal, described in Exporting the Installed TLS Certificate, and install it on this portal, described in Importing a TLS Certificate.
When generating a certificate request and installing the received certificate, the private key is generated on the portal and never leaves it. In contrast, when exporting and importing certificates, the private key is exported and imported along with the certificate, and it is therefore important to keep the exported file confidential.